In a world where attackers evolve at an unprecedented speed, an advanced Zero-Trust approach is a fundamental pillar for your protection.
ZTNA (Zero-Trust Network Access)
A paradigm shift for your security strategy, based on the principle of continuous connection verification.
It reduces the risk of security breaches, protects digital assets, and maintains operational continuity in an increasingly distributed and dynamic work environment.
IAM(Identity and Access Management)
Thanks to a strategic and best-practice approach, only authorized individuals will have access to sensitive resources and data.
We provide you with advanced tools for managing and monitoring privileged access (PAM), ensuring granular control and complete visibility over who has access to what
Secure Access Service Edge
You'll ensure comprehensive and continuous protection of applications and data, wherever users are located.
By integrating security and networking into a single cloud-based platform, SASE allows you to implement consistent and scalable security policies across all devices and locations.
Cloud Access Security Broker
Monitor and protect access to cloud applications, prevent internal and external threats, and ensure regulatory compliance for your users
You'll fully leverage the benefits of the cloud in terms of flexibility and productivity without compromising data security.
Secure Web Gateway
Smart working has increased the need to protect employee web Browse.
With our solutions, you can filter web traffic in real-time, block access to malicious or non-compliant websites, and identify and block cyber threats.
Endpoint security
Reduce the risk of security breaches and protect sensitive data wherever users are located.
Our endpoint security solutions (EDR, XDR), integrated with our analysis, detection, and mitigation services (MDR), offer advanced defense against malware, ransomware, and other cyber threats.
Application and Workload Security
Using advanced application protection and threat detection techniques, we protect applications and workloads both on-premise and in the cloud, ensuring regulatory compliance and business continuity.
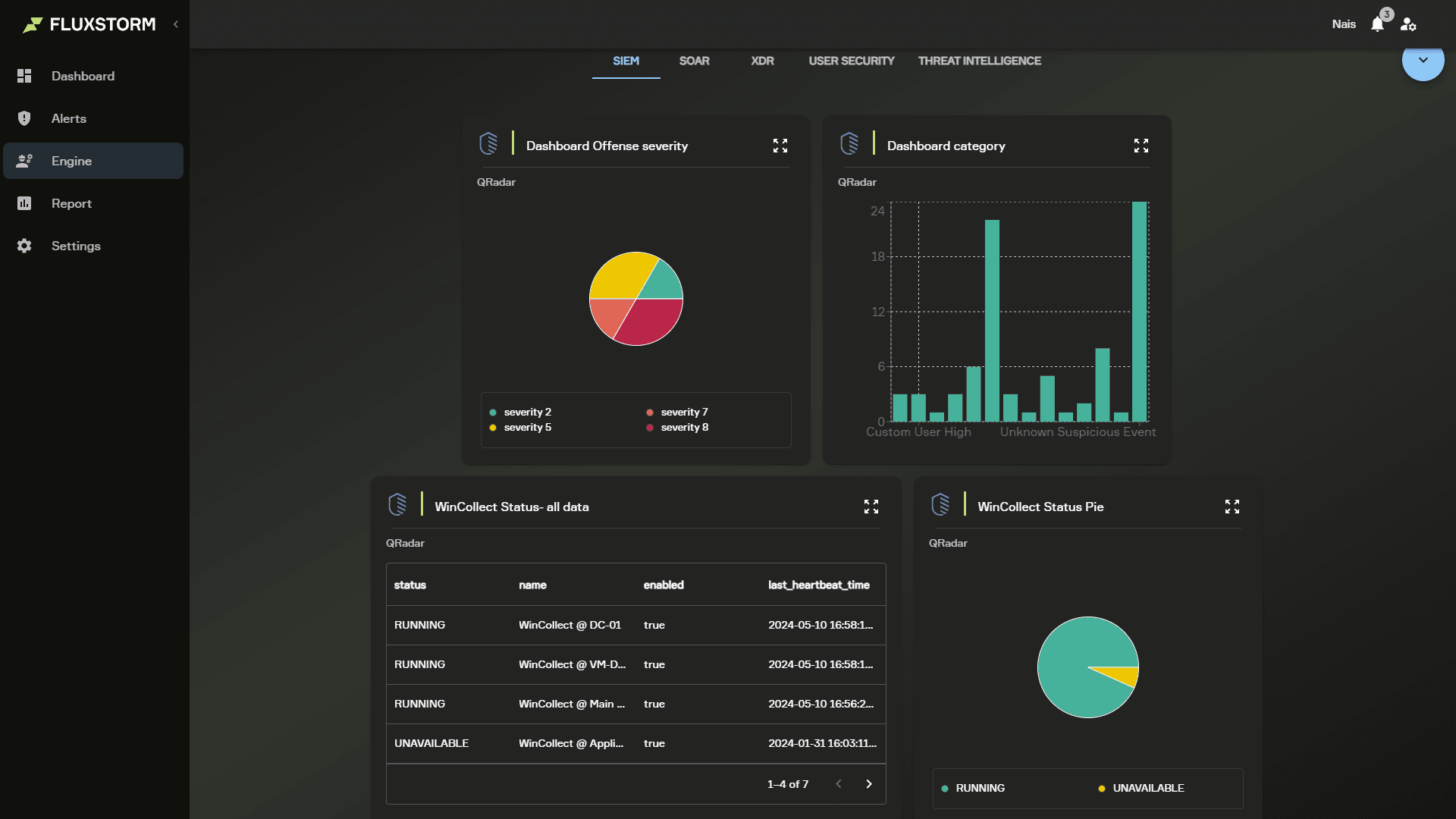
Integrate your Zero-Trust approach and technologies through Fluxstorm. We guarantee you full control and visibility over your security operations.