Single point of governance, real-time, 24/7
Vertical expertise for top-tier safety, compliance and transparency.
Technologies
We integrate with leading technologies, maintaining an agnostic approach, and adapting to client needs.
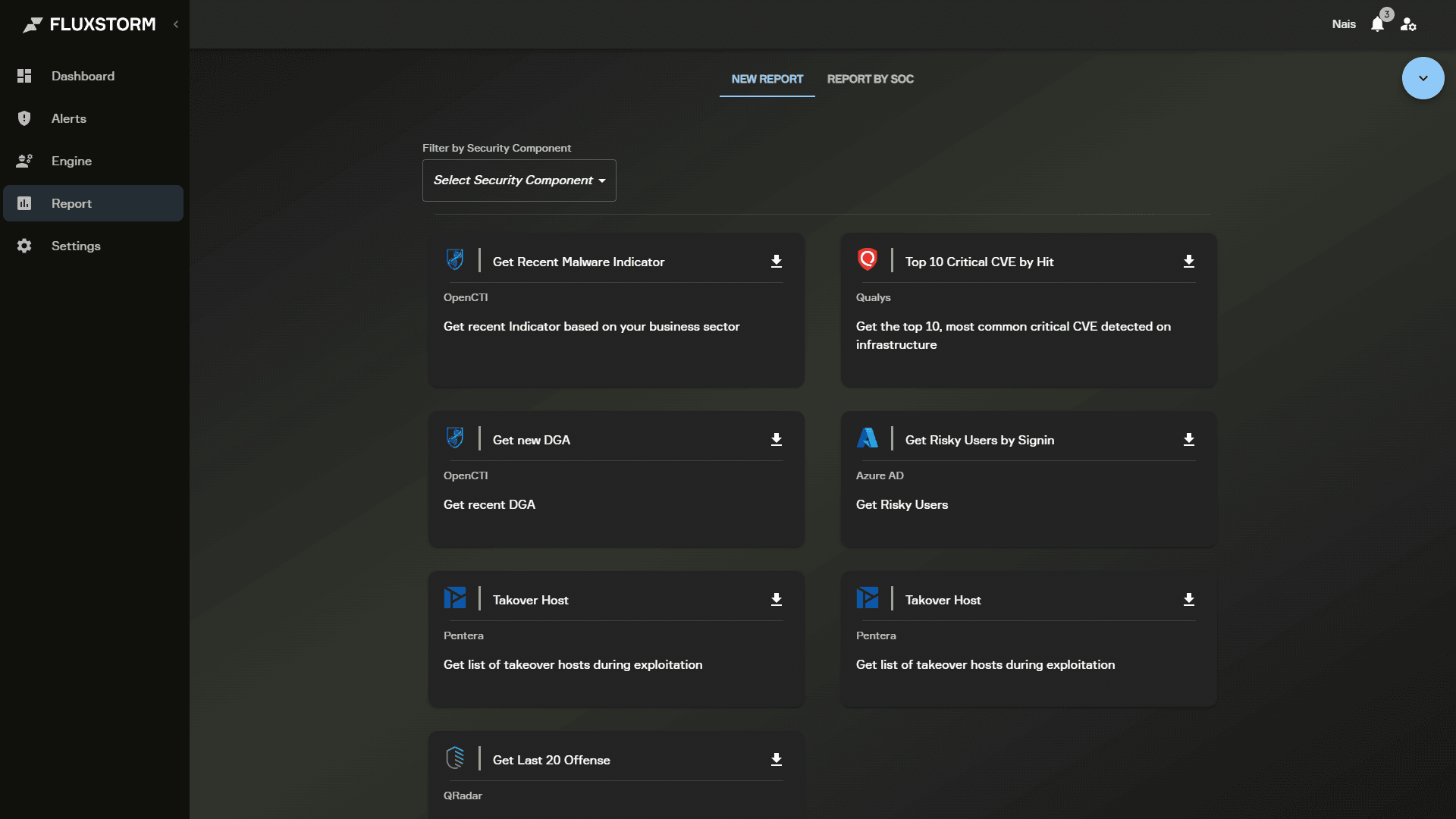
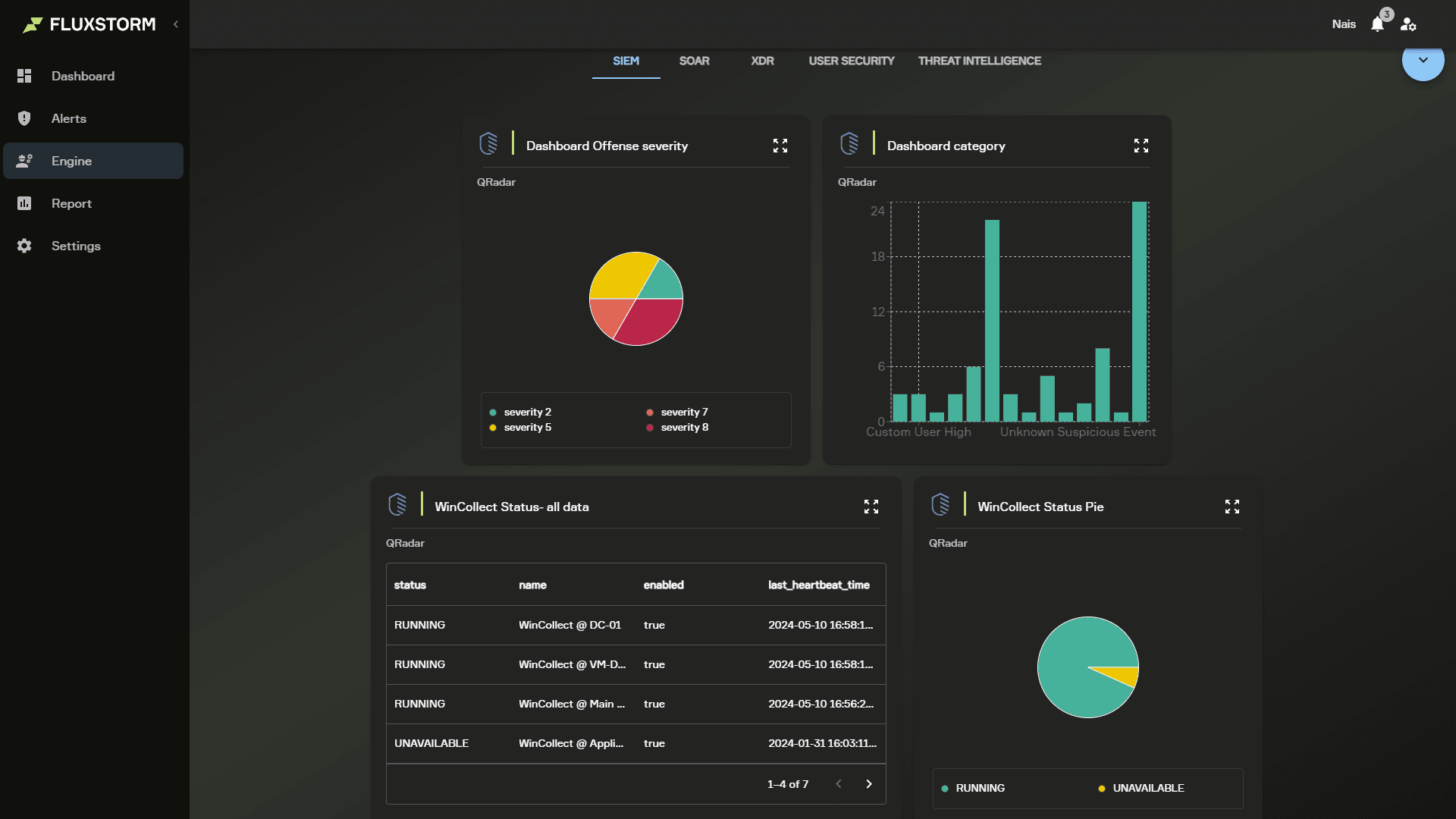
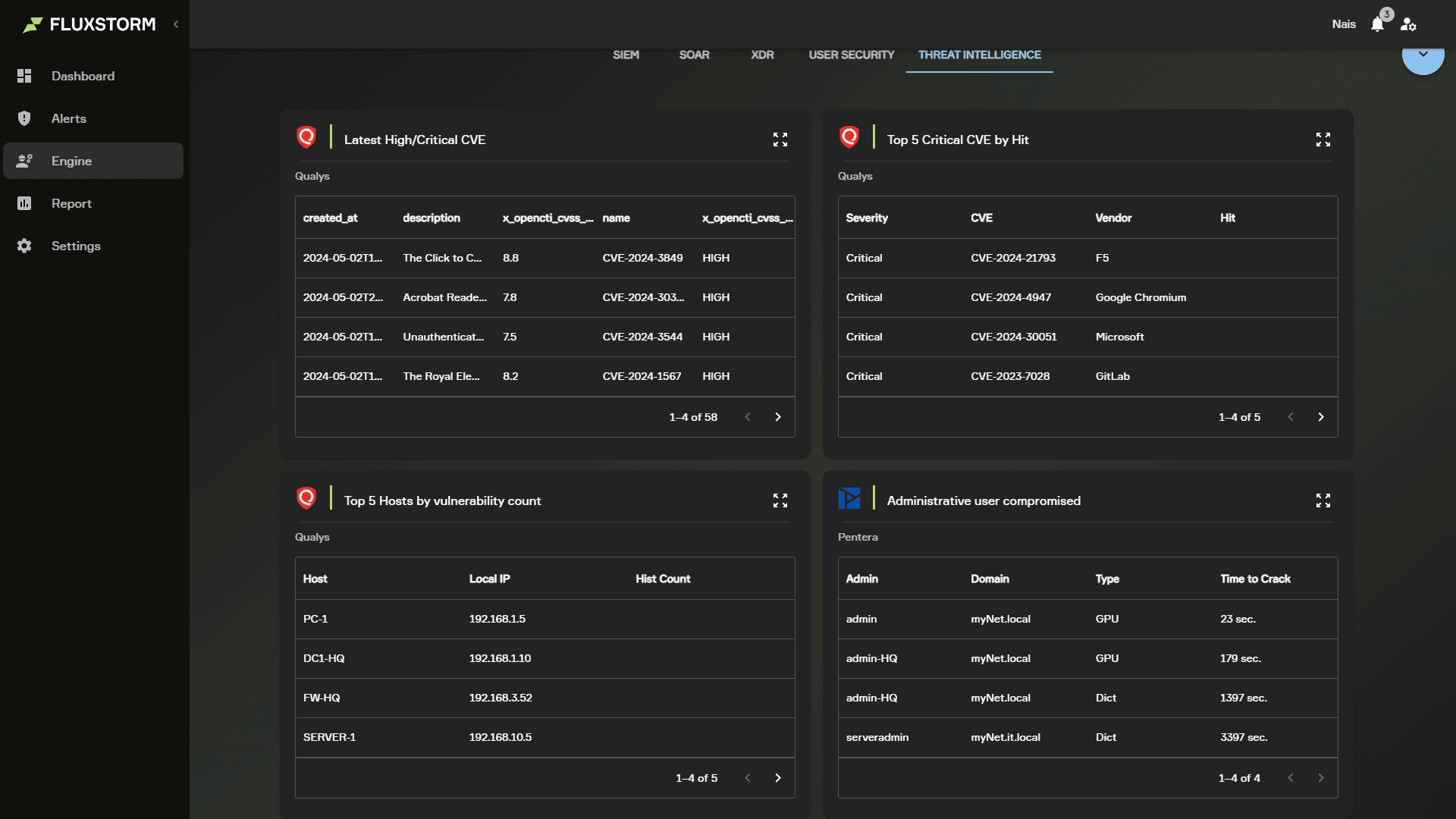
User Interface
An intuitive interface that provides a real-time view of our security operations.
A comprehensive suite of services designed to provide your business with the highest level of security.
Security Operations Center 24/7
Continuous monitoring for constant infrastructure protection.
Advanced Containment
Rapid and strategic response to threats to limit their impact.
Incident response
Planned actions to manage and mitigate the consequences of security incidents.
Advanced incident analysis
In-depth root cause identification to enhance preventive measures.
Vulnerability Assessment
Proactive identification of system vulnerabilities.
Penetration test
Simulated attacks to evaluate network security.
Security Validation
Periodic verification of the effectiveness of implemented security controls.
Dark Web Monitoring
Monitoring of the dark web to detect targeted illicit activities.
Takedown Service
Quick removal of malicious content and fraudulent domains.
VIP Protection
Tailored protection for key figures within the organization.
Ready to Respond.
The increase in security incidents and their growing complexity demand a radical change in the way traditional SOC services are managed.
- Enhancement of automation through Machine Learning engines
- Native orchestration of backend technology stacks (SIEM, EDR, XDR, etc.)
- Real-time Visibility, 24/7, over all critical eventsrelated to your IT&OT infrastructure
- Dedicated chat with our Security Analysts.
- Service Report Archive
- Compliance reporting management (NIS2, GDPR, NIST, TISAX, DORA)
Comprehensive Prevention.
Incident management requires granular knowledge of the vulnerabilities affecting monitored services. This is why we have identified prevention as one of the core pillars of Fluxstorm.
- Vulnerability Assessment
- Infrastructure and Application Penetration Testing
- Security Posture Assessment
- Native integration with Fluxstorm Response and Visionary to give you extensive and centralized visibility on a single platform
Looking to the future.
Being able to predict incidents has become essential and requires deep contextual knowledge, extended to indicators of compromise that are not yet confirmed as real attacks, targeting the technologies used by your company and its supply chain.
- Early Warning Services
- Threat Intelligence
- Dark Web Monitoring
- Extended protection for VIP user and your brand